Penetration Testing Services
Outpost24 offers penetration testing services on networks, web, and mobile applications. Our in-house team of highly skilled ethical hackers will review your environment from a hacker’s perspective to uncover blind spots, exploitable vulnerabilities, and logic errors. Insights gathered from our testing services can be used to verify the effectiveness of your security controls, minimize security gaps, and support compliance requirements.
Our Penetration Testing Services
Go beyond vulnerability scanners with our classic penetration testing services. Outpost24 offers in-depth penetration testing tailored to your business needs. The security assessment includes a comprehensive report with a detailed outline of the uncovered issues, including risk level and actionable guidance for remediation. We will help you better understand how these issues could increase your risk of a cyberattack, and best practice for improving security measures.


Network & Infrastructure Assessments
We offer network infrastructure tests on internal, external and wireless networks. These are manual tests performed by our team using a variety of penetration techniques and tools.

Web Application & API Assessments
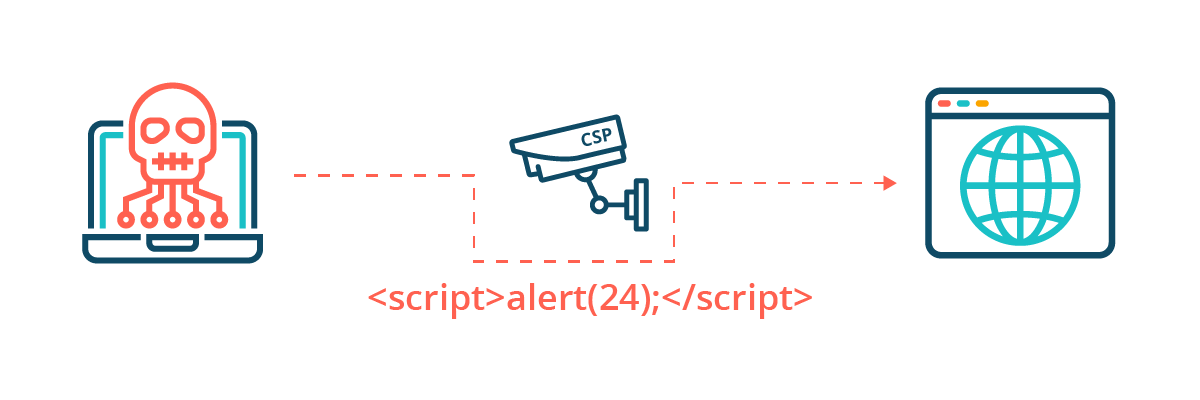
We offer in-depth web application testing for technical (e.g. SQL Injection, XSS) and business logic (e.g. negative quantity in a web shop order) flaws against OWASP Top 10.

Mobile Application Assessments
We offer a complete assessment of your mobile application to identify security issues that can endanger your users, expose sensitive information, and cause reputational damage.
Pen Testing Certifications
- Certified Azure Red Team Professional (CARTP)
- Certified Information Systems Security Professional (CISSP)
- The Council for Registered Ethical Security Tester (CREST)
- Certified Red Team Professional (CRTP)
- Certified Red Team Operator (CRTO)
- eLearnSecurity Certified Professional Penetration Tester (eCPPT)
- eLearnSecurity Web Application Penetration Tester (eWPT)
- eLearnSecurity Web Application Penetration Tester eXtreme (eWPTX)
- Exploit Researcher and Advanced Penetration Tester (GXPN)
- OSSTMM Professional Security Tester (OPST)
- Offensive Security Certified Expert (OSCE)
- OffSec Certified Professional (OSCP)
- OffSec Web Expert (OSWE)
Frequently Asked Questions
A penetration test is an authorized simulated attack on a computer or physical system, performed by penetration testers, to evaluate the security of the system. Penetration testing is often used to complement an organization’s vulnerability management process to ensure security hygiene for better risk management. A penetration test is instructed by an organization on a predefined scope and objective.
Penetration testing is an effective way to detect and remediate flaws in your infrastructure before they turn into a serious threat to your business. It can also be used to report regulatory obligations such as PCI, HIPAA, Sarbanes-Oxley or internal policy compliance like CIS controls.
The length of a penetration test depends on the scope and size of your organization: a network penetration test can take around 2-3 days, applications that require processing vast amounts of data can take up to 10 days, and larger scale physical assessments can take several weeks.
Penetration testing and red teaming serve different purposes, and are dependent on an organization’s security maturity, and testing goals. Penetration testing takes a more general approach by finding and exploiting as many vulnerabilities as possible, in a given timeframe. Red Teaming is a scenario-based attack simulation that will test an organization’s detection and response capabilities against various attacks like ransomware and phishing attempts to provide actionable recommendations for improvements.
CREST is a certification body representing the information security industry. All CREST member companies must undergo a rigorous assessment of their services, processes, and quality to ensure consistency of knowledge against the evolving security backdrop. Outpost24’s SWAT, pen testing as a service for web application security testing, is CREST certified.
Success Stories
Success stories and real-world examples of how SWAT is helping businesses improve their security posture, without slowing down development.
Get a Quote
Please fill in your information to get in touch with our security experts. All fields are mandatory.